We hope you like reading this blog post.
If you would like to speak to the Boost IT team about completing an Essential 8 cyber security implementation for you, click here.
Boost IT partners with the Australian Cyber Security Centre through the Joint Cyber Security Centre (JCSC) program.
In today’s digital age, cybersecurity is more crucial than ever. Cyber threats are evolving, becoming more sophisticated and frequent. Organisations must adopt proactive measures to safeguard their data and systems.
The Essential Eight cybersecurity framework offers a robust solution. Developed by the Australian Cyber Security Centre, it provides a set of strategies to mitigate cyber risks. These strategies are designed to be adaptable and scalable, fitting various organisational needs.
Implementing the Essential Eight can significantly reduce the risk of cyber incidents. It emphasises proactive security measures, focusing on prevention rather than reaction. This approach helps organisations stay ahead of potential threats.
The framework is recognised globally as best practice. It serves as a cybersecurity checklist, ensuring critical security areas are covered. By following the Essential Eight, organisations can enhance their cybersecurity posture and protect their assets effectively.
Understanding the Essential Eight cybersecurity framework
The Essential Eight cybersecurity framework is a strategic approach to combating cyber threats. It was created to provide organisations with a practical roadmap for enhancing their security posture.
This framework consists of eight key mitigation strategies that are crucial for preventing cyber incidents. These strategies are designed to tackle the most common cyber threats, providing a comprehensive defence mechanism.
Here’s a brief list of the strategies included in the Essential Eight framework:
- Application control (whitelisting)
- Patch applications
- Configure Microsoft Office macro settings
- User application hardening
- Restrict administrative privileges
- Patch operating systems
- Multi-factor authentication (MFA)
- Regular backups
Each strategy is aimed at addressing specific vulnerabilities and strengthening the organisation’s cybersecurity defences. They offer a layered security approach, ensuring multiple protective measures are in place.
Organisations of all sizes and industries can implement the Essential Eight. It is structured to be flexible, allowing customisation to meet varying risk profiles and operational contexts. This adaptability makes it a valuable tool in the ever-changing cybersecurity landscape.
The most effective cyber security mitigation strategies
Of Australian cyber attacks officially reported, a huge 90% impact small businesses. Considering this staggering figure, it’s no surprise that 70% of small to medium-sized businesses nationwide have weak to no security and are specifically targeted by cybercriminals across a digitally connected global network.
If you fit this business profile, now is the time to take stock, evaluate your current cyber security position and take cost-effective measures to prevent a serious breach. It’s not only the immediate financial impacts that affect your business; there are a host of other negative repercussions, including productivity downtime, reputational damage and employee frustration, to name a few.
This Boost IT article will walk you through the unpredictable world of domestic cyber security threats in easy-to-understand language. We’ll show you how to adopt the Australian Government-recommended Essential Eight mitigation strategies to pinpoint the baseline IT systems and protocols you need to avoid costly cyber security incidents.
Australian cyber security statistics
The cyber threat landscape we face shows improved awareness and cyber security capabilities, but the threat and sophistication is growing.
Video: A clear picture of the top cyber threats and cyber security incidents affecting Australia – ASD Gov AU
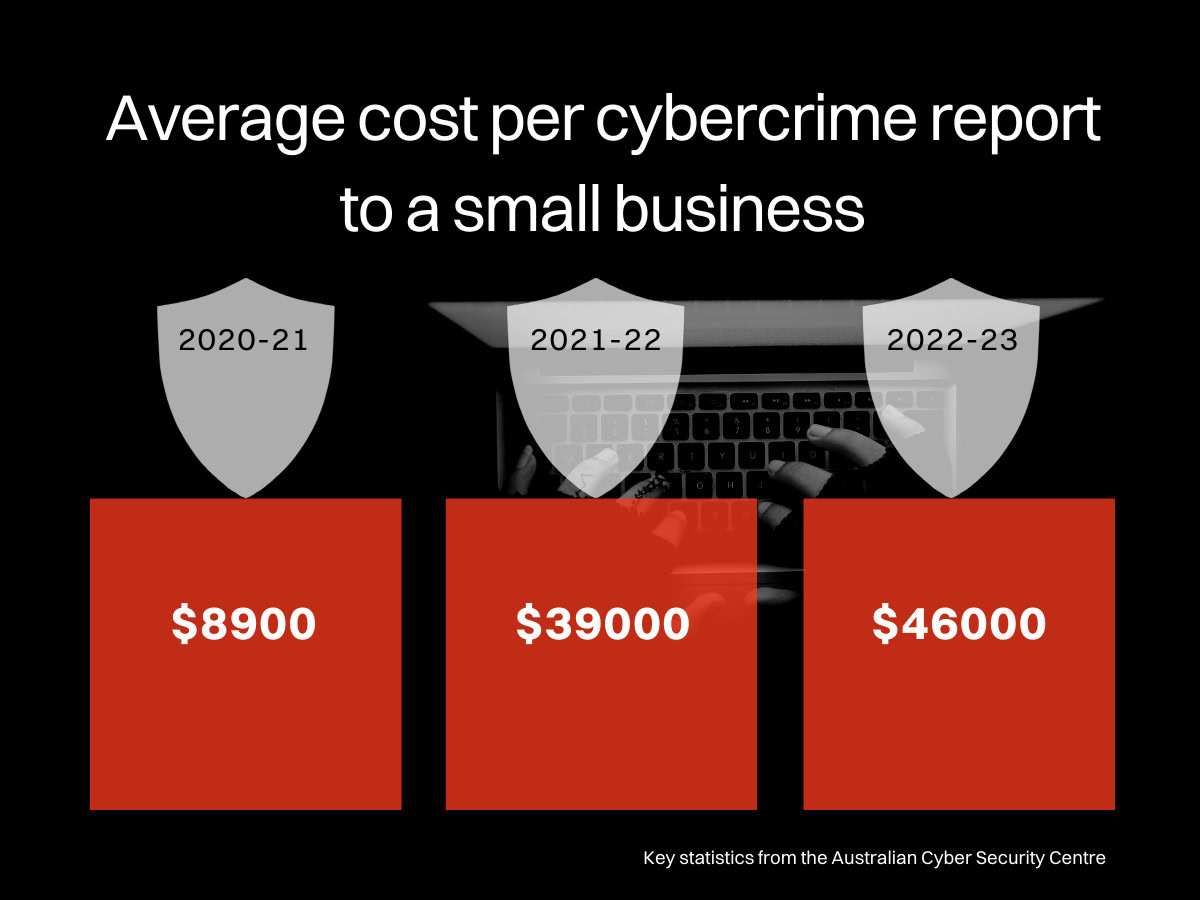
Above: 3-year trend of average cost to small businesses.
Reports: 2024/2025 Annual Cyber Threat Report
Table of contents
Click the links below to move quickly to that section.
⇓ What is the Essential 8 cyber security?
⇓ Phase One — Prevent malware delivery and execution
⇓ Phase Two — Limit cyber security incidents
⇓ Phase Three — Recover data and system availability
⇓ The Essential 8 Maturity Model: Levels and Assessment
⇓ Implementing the Essential Eight: Step-by-Step Cybersecurity Checklist
⇓ Overcoming Common Challenges in Essential Eight Adoption
⇓ 3 Practical Ways to Protect Your Business
⇓ What should you do if your small business is compromised?
⇓ How to notify your affected customers of a severe cyber security breach
What is Essential Eight cybersecurity
The ASD developed the Essential Eight to help organisations protect their internet-connected information technology networks against cyber threats through a clear list of mitigation strategies.
There are many technical solutions to prevent malicious software attacks on your business, and the Australian Government prescribes the Essential Eight mitigation strategies as a robust measure for protection that’s tried and tested by notable companies and organisations of all sizes.
If you’re an Australian business currently working with the Australian Government Department of Defence or seeking to partner with them, you must additionally have the ASD Essential Eight cyber standard via stringent DISP accreditation.
Let’s now explore the eight individual mitigation strategies a little deeper to better understand this cyber security defence.

Phase One — Prevent malware delivery and execution
The first phase of Essential Eight cyber security is enlisting a foundational shield to block the intrusive brunt of sophisticated cyber attacks. Whether cybercriminals initially launch phishing attacks, hacking or malware, there are four Essential Eight mitigation strategies to put in place for protection.
- Application control: prevents unapproved and possibly harmful programs from installing and running on your computer systems.
- Patch applications: protects your technology from newly identified threats by always using the latest version of an application.
- Configure Microsoft Office macro settings: only permits trusted machines and individuals to access your business’ data from the internet.
- User application hardening: turns off unneeded features over various platforms (e.g. your web browser and Microsoft Office) as the less open you are, the fewer points of attack entry into your business — blocking ads and internet promotions also occur at this point.
Phase Two — Limit cyber security incidents
Unfortunately, there may be times when you can’t prevent a sophisticated cyber attack, as some are highly intuitive by design, ingeniously targeting system weak points. A critical step you can take is to ensure a cyber breach doesn’t extend its damage too far, like installing viruses or stealing sensitive data. This phase two stage recommends three Essential Eight mitigation strategies to put in place for future protection.
- Restrict administrative privileges: your operating system should be programmed to only allow specific individuals access to sensitive information. These administrative privileges should be regularly revalidated, and privileged accounts should not be used for casual web browsing, email checking or working remotely in insecure Wi-Fi environments.
- Patch operating systems: constantly updating your computer and network devices to the latest operating system protects them from the latest cyber threats.
- Multi-factor authentication: passwords are easily hacked, so they should be made secure with extra identification proof, especially when working remotely or accessing essential and sensitive data.
Phase Three — Recover data and system availability
When your cyber attack involves ransomware or your data has been corrupted, recovering a previous version of your latest data may be the only thing you can do to keep your business running. Phase three recommends a last resort Essential Eight mitigation strategy to put in place for protection.
- A daily backup system: your essential new and changed data should be backed up, with software and configuration settings stored safely and disconnected from your system to avoid risk. You must also identify your essential and sensitive data and determine the retention period of each — finance information might need seven years, while configuration settings only require three months. Regular testing of your restoration backup is also critical to ensure ongoing compliance and protection.
The Essential 8 Maturity Model: levels and assessment
The Essential 8 Maturity Model provides a structured way to assess cybersecurity capabilities. It defines levels of maturity, enabling organisations to gauge their implementation progress.
The model includes three distinct levels. Each level represents an increasing degree of cybersecurity sophistication. Organisations can progressively improve their security posture by advancing through these levels.
Maturity levels
Level 1: Basic controls are implemented but might not be monitored or enforced systematically.
Level 2: Controls are applied more consistently, with some degree of monitoring and enforcement.
Level 3: Advanced control measures are in place, demonstrating a robust, well-managed security environment.
Assessing maturity involves evaluating controls against predefined criteria. This helps identify gaps and areas needing improvement. The goal is continuous enhancement of security measures.
Tailored assessments consider organisational risks and resources. This customisation ensures the maturity model is practical and achievable for any organisation. By progressing through maturity levels, organisations can proactively manage and mitigate cybersecurity risks.
Implementing the Essential Eight: step-by-step cybersecurity checklist
Implementing the Essential Eight requires a strategic approach. Begin by understanding your organisation’s unique needs and risk profile. Tailor the framework to fit these specific requirements.
A phased implementation approach can be beneficial. This allows for a gradual integration of controls, minimising disruption. Prioritise high-impact strategies to address immediate vulnerabilities.
Cybersecurity checklist:
- Identify critical assets and vulnerabilities: Understand what needs protection first.
- Set a baseline for security practices: Establish fundamental controls as stepping stones.
- Implement each of the eight controls systematically: Prioritise based on impact and ease of deployment.
- Conduct regular reviews and updates: Adapt to evolving threats and improve continuously.
- Engage stakeholders across the organisation: Foster a culture of awareness and responsibility.
Ensure adequate training and awareness for staff. Regular audits and adjustments are key to sustaining improvements. This proactive approach ultimately strengthens your organisation’s cybersecurity posture.
Overcoming common challenges in Essential Eight adoption
Adopting the Essential Eight is not without its hurdles. One key challenge is balancing security needs with business operations. Organisations often struggle to integrate controls without disrupting workflows.
Resource constraints can aso be a roadblock. This involves both financial limitations and a shortage of skilled personnel. Finding the right balance is crucial to success.
Common challenges:
- Limited budget allocations: Prioritising investments in the most impactful areas is essential.
- Resistance to change: Employees may resist new procedures due to a lack of understanding.
- Technological constraints: Legacy systems may not support all recommended controls.
To overcome these challenges, focus on fostering a culture of security awareness. Investing in training and clear communication will help smooth the transition and encourage compliance.
Three practical ways to protect your business
Not that we advocate for skipping any Essential Eight mitigation strategies where possible; we understand that some small businesses might not have the resources to apply their relevant maturity level. If this is the case, you should instate a few simple protections as a cyber security priority at the very minimum. Here’s how.
1. Implement daily backups
To avoid risk, your essential data should be backed up daily, with software and configuration settings stored safely and disconnected from your system. It’s also paramount to regularly test your restoration backup to ensure operational reliability and protections are always in place. Contact a Boost IT technician today who can tailor-make a fail-safe system for your small business cyber security needs.
2. Use a cloud-managed antivirus with patch management
Most businesses now operate their IT on the Cloud and are at greater cyber security risk if they don’t install the most appropriate antivirus software for protection. This itself isn’t enough, though. You must stay diligent and update your cyber security antivirus software, as an outdated version on any system or machine is an easy penetration target for malicious code. With Boost IT, our technicians will proactively inform you that a software update is needed to counteract any new cyber security threats.
3. Multifactor authentication
Relying on a single security password isn’t safe anymore, as it only takes a savvy cybercriminal 5 seconds to hack an eight lowercase letter password with brute technical force. Some people conveniently decide to use the same password over various platforms, making hacking an even easier exercise for them. We recommend installing an extra authentication method requiring additional identification proof to avoid this type of breach, especially when working remotely or accessing essential and sensitive data. Boost IT can easily set up multifactor authentication for your team that’s simple to apply, with only minutes of online training needed.
Building a proactive cybersecurity culture
Incorporating the Essential Eight into your cybersecurity strategy offers robust protection against cyber threats. These strategies provide a clear roadmap to follow, helping organisations enhance their security posture.
A proactive cybersecurity culture emphasises prevention. By integrating the Essential Eight, businesses can mitigate risks before they become problems.
Next steps
Boost IT can help you identify the weak points of your IT and implement a plan of action.

